Cyber Briefing: 2025.08.29
Docker flaw hijacks host, Blind Eagle hits Colombia, Tamperedchef malware, HCSG, TransUnion & Salvation Army breaches, VerifTools seized, CrowdStrike deal, DPRK crypto sanctions.
👉 What's happening in cybersecurity today?
Welcome to Cyber Briefing, the newsletter that informs you about the latest cybersecurity advisories, alerts, incidents and news every weekday.
First time seeing this? Please Subscribe
🚨 Cyber Alerts
1. Docker Desktop Flaw Allows Host Hijack
A critical server-side request forgery (SSRF) vulnerability, identified as CVE-2025-9074, has been discovered in Docker Desktop for Windows and macOS. This flaw allows a malicious container to compromise the host system by accessing the Docker Engine API, even with the Enhanced Container Isolation (ECI) feature enabled.
2. Blind Eagle Clusters Target Colombia
Cybersecurity researchers have identified five distinct campaigns by the threat actor Blind Eagle, also known as TAG-144, spanning from May 2024 to July 2025. These attacks primarily targeted Colombian government entities, leveraging a mix of cyber espionage and financial motivations to compromise various sectors across South America.
3. Tamperedchef Malware Masquerades As PDF
Cybersecurity researchers have uncovered a new cybercrime campaign that uses malicious advertising to trick victims into downloading a trojanized PDF editor containing a new information-stealing malware called TamperedChef. This malware harvests sensitive data like credentials and web cookies from victims' computers.
For more alerts, click here!
💥 Cyber Incidents
4. Healthcare Services Group Data Breach
In 2024, Healthcare Services Group (HCSG) suffered a data breach that exposed the personal information of over 624,000 individuals, with hackers accessing and copying sensitive files from the company's systems between September 27 and October 3. While HCSG has offered 12 months of free credit monitoring, it took nearly a year to begin notifying affected individuals, raising concerns about the delay and potential legal ramifications.
5. Transunion Reports Data Breach Impact
Credit reporting agency TransUnion recently disclosed a data breach that affected over 4.4 million customers' personal information, including names, dates of birth, and Social Security numbers. The breach, which occurred on July 28, was caused by unauthorized access to a third-party application used for the company's U.S. consumer support operations.
6. Salvation Army Data Breach Notification
The Salvation Army is notifying victims of a May 2025 data breach that exposed personal information, including names, Social Security numbers, and driver’s license numbers. The ransomware group Chaos, which emerged in 2021, has claimed responsibility for the attack, although the Salvation Army has not confirmed this claim.
For more incidents, click here!
📢 Cyber News
7. Feds Seize Veriftools Fake ID Marketplace
Authorities from the Netherlands and the United States have dismantled VerifTools, an online marketplace that sold fraudulent identity documents, after a multi-year investigation revealed it was used by cybercriminals to bypass identity verification systems and access online accounts. Despite the takedown, the marketplace's operators have already resurrected the service on a new domain, demonstrating the ongoing challenge of disrupting such illicit operations.
8. Crowdstrike To Acquire Onum For $290M
CrowdStrike announced it will acquire Onum for $290 million to enhance its Falcon Next-Gen SIEM platform. The acquisition aims to improve data processing for AI-driven security operations by integrating Onum's real-time telemetry pipeline management technology.
9. US Treasury Sanctions DPRK Crypto Scheme
The U.S. Treasury's Office of Foreign Assets Control (OFAC) has imposed new sanctions on individuals and entities involved in a North Korean scheme that uses remote IT workers to generate illicit funds for the country's weapons programs. This operation, which uses fraudulent identities and AI-powered tools, has allowed North Korean agents to infiltrate U.S. and other companies, stealing data and extorting businesses.
For more news, click here!
📈Cyber Stocks
As trading unfolded on Friday, August 29, 2025, cybersecurity stocks closed the week with a broadly positive tone as earnings strength and sector recognition outweighed macro caution.
Radware (RDWR) closed at $25.88, gaining modestly as investors responded positively to its recognition as a leader in web application and API protection, while valuation concerns remained in focus.
Rapid7 (RPD) ended at $20.90, moving higher as confidence in its position within threat exposure management supported buying interest.
Check Point Software Technologies (CHKP) settled at $191.26, edging up on consistent post-earnings momentum and stable operating margins.
SentinelOne (S) finished at $17.61, rising strongly after Q2 earnings highlighted robust ARR growth and reinforced optimism around its AI-driven security platform.
CrowdStrike (CRWD) advanced to $442.00, rebounding as investors weighed mixed guidance against solid ARR growth, long-term potential from its Onum acquisition, and supportive analyst outlooks.
💡 Cyber Tip
📄 Beware Fake PDF Editors Installing TamperedChef Malware
Cybercriminals are using malicious ads to trick users into downloading trojanized PDF editors, such as the fake AppSuite PDF Editor, which secretly installs the TamperedChef infostealer. This malware waits weeks before activating, then steals credentials, cookies, and sensitive data from browsers while maintaining persistence through backdoors.
✅ What you should do
Only download PDF editors and software from official vendor websites or trusted app stores
Be cautious of ads promoting free or unknown PDF tools
Regularly review installed programs and uninstall any suspicious or unnecessary apps
Use endpoint protection to detect malware that hides in legitimate-looking software
Monitor browser activity for unusual changes, such as altered search engines or unexpected logouts
🔒 Why this matters
TamperedChef highlights the growing danger of malvertising, where criminals abuse trusted ad platforms to distribute malware at scale. Because the malware delays activation, it can infect thousands of systems before detection. Vigilance in software downloads is critical to avoid compromise.
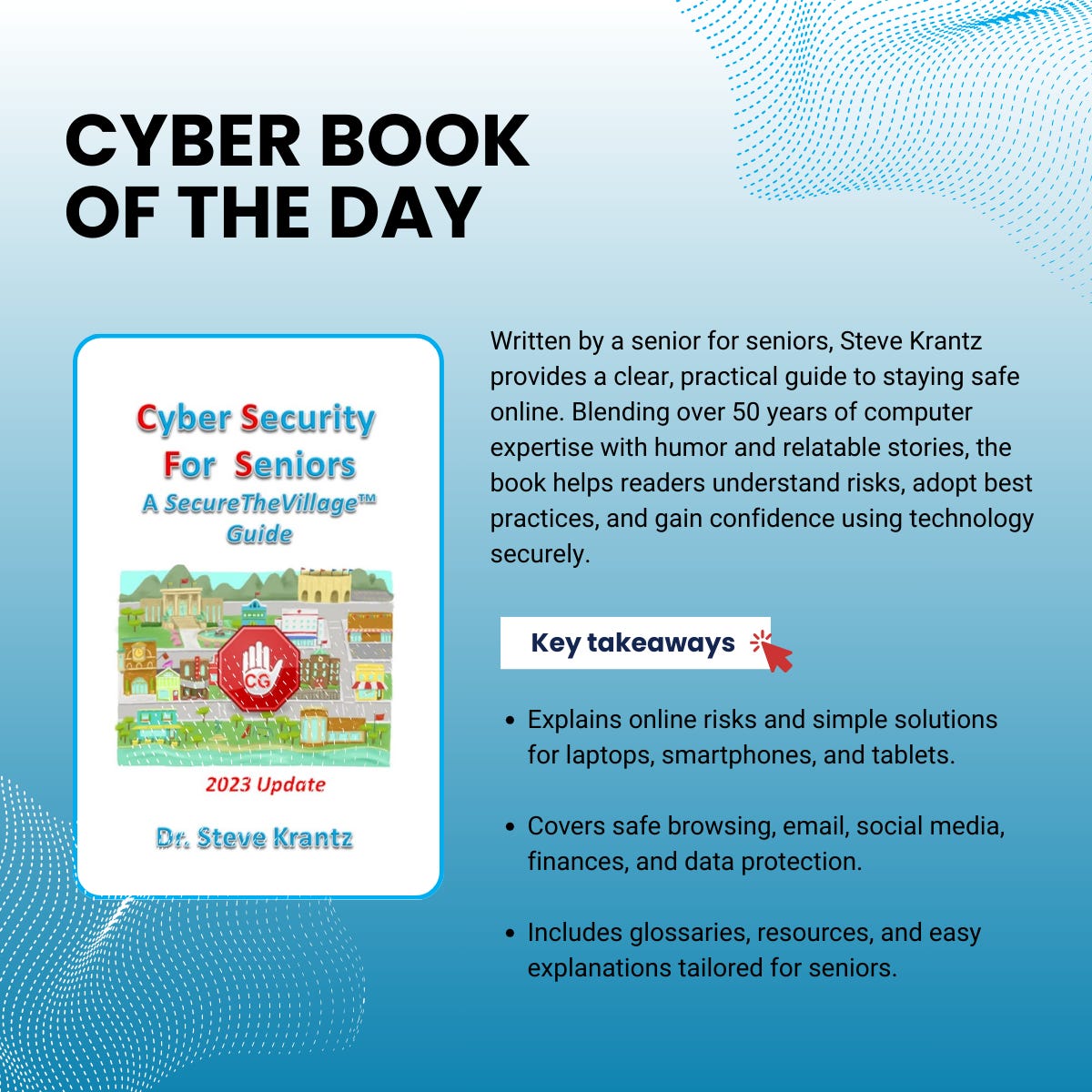
📚 Cyber Book
Cyber security for seniors by Steve Krantz
That concludes today’s briefing . You can check the top headlines here!
Copyright © 2025 CyberMaterial. All Rights Reserved.
Follow CyberMaterial on:
Substack, LinkedIn, Twitter, Reddit, Instagram, Facebook, YouTube, and Medium.